Troubleshooting Security Groups on AWS for Callaba and Streaming Instances
One of the most common AWS launch problems is simple: the instance is running, the public IP exists, but the dashboard does not open. In most cases, that happens because the security group was not created correctly or the required inbound rules were never added.
This page focuses on the fastest troubleshooting path: find the right instance, inspect its security group, confirm the inbound rules, and fix the access policy without changing unrelated AWS settings. If your public IP changes after restart, pair this with Elastic IP setup. If you are still at the initial launch stage, start with Callaba Cloud on AWS.
What a security group does in practice
A security group is the traffic gate in front of the instance. If the right inbound rule is missing, the service can be healthy on the machine and still look completely unreachable from the outside.
Step 1. Confirm that the instance is actually running
Before changing rules, make sure you are looking at the correct EC2 instance and that it is in the running state.

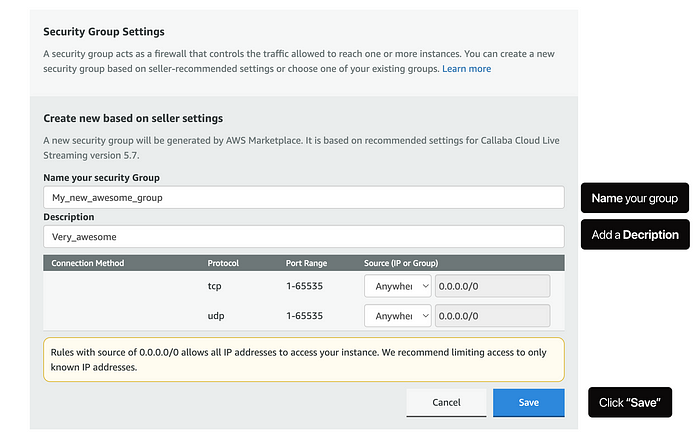
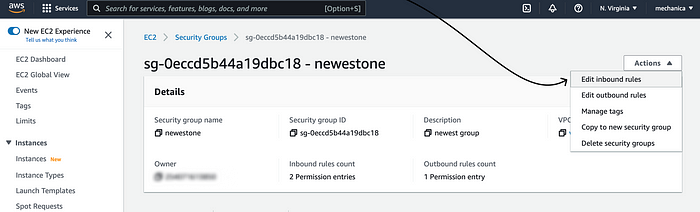
Step 2. Open the attached security group
From the instance details, open the security group linked to that instance. This is where inbound and outbound traffic policy is defined.
Step 3. Inspect the inbound rules
Check whether the required inbound ports are actually allowed. For dashboard access, HTTP or HTTPS rules are often the first thing to verify. If the machine also handles ingest or other media workflows, confirm that those ports are planned intentionally and not assumed to be open.

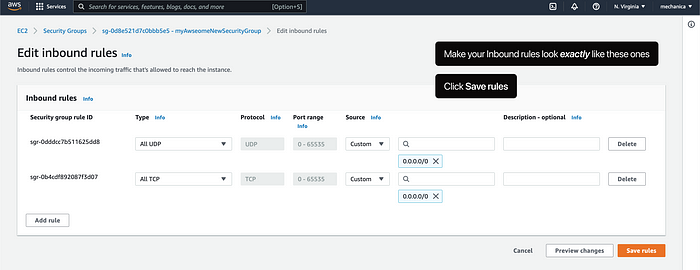
Step 4. Edit the rules if needed
Add or correct the inbound rules so the dashboard and required workflow ports are reachable from the sources that should access them.

Step 5. Save and retest from the public address
After saving the rule changes, retry the dashboard or endpoint using the public IP. If the security group was the real issue, access usually starts working immediately.
What usually causes the problem
- the wrong security group is attached to the instance
- the inbound rule for the dashboard was never added
- the source is too restrictive or simply incorrect
- the instance has the right rules but the team is testing the wrong IP
If the rules look correct and the instance is still unreachable, the next things to check are the public IP, route design, and whether the application on the instance is actually listening as expected.
Final practical rule
When an AWS streaming instance looks alive but unreachable, check the security group before assuming the application is broken. A missing inbound rule is a much more common failure than a dead media stack.
